Future-Proof Your Email Encryption with Biometrics

It seems that one of the biggest roadblocks in staying secure online is the balance between user experience and strength of security.
With the remote work, increased expectations around data privacy and seamless digital experiences, the need for secure information exchange has never been higher – but so is the number of passwords the average person must remember.
Security vs Ease of Access
Security vs ease of access is a common issue amongst most tech leaders – 98% of which reported that their employees find opening encrypted emails and documents frustrating, according to our survey conducted by Gartner in 2022.
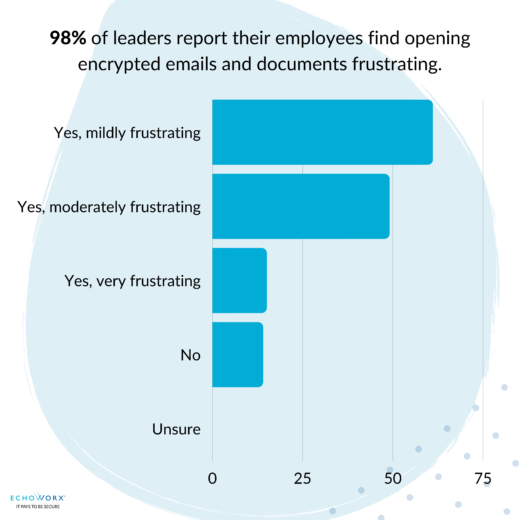
With these frustrations over complicated processes and additional steps in accessing encrypted information, 50% of employers reported that their organization is looking to ease access to secure messages and documents. Between cumbersome login processes and too much additional overhead to manage, most leaders agreed that user acceptability was the most important aspect of their authentication process – even more so than privacy and security requirements.
But that doesn’t mean that security isn’t a factor in the decision-making process. In fact, 95% of respondents reported that they were concerned about security risks from increased use of digital communications.
Survey: Trends Shaping the Future of Email Encryption Access
A ‘Best of Both Worlds’ Solution
Utilizing biometrics and offering third-party social logins creates a ‘best of both worlds’ solution to security concerns and frustrations with opening encrypted information. Although these alternatives secure and simplify encrypted information, 42% of tech leaders were concerned about offering third-party social login options, like those offered by Google or Microsoft. IT and security leaders cited lack of research and trust as reasons to hesitate when it comes to implementing login alternatives.
Despite these concerns, the consensus from respondents was positive towards the use of social and biometric login options, with emphasis on their benefits of improved security adoption, services, and more user-friendly
MFA (Multi Factor Authentication) at the top of the list. The balance between user experience and security strength seems to find equilibrium with the option of social and biometric logins; creating a more efficient, yet secure experience.
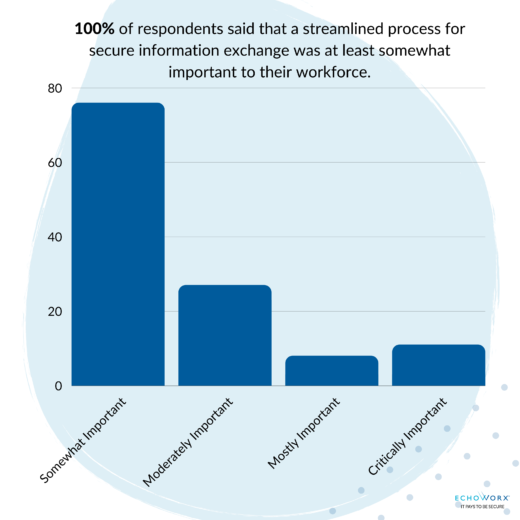
With 100% of IT leaders surveyed reporting that a streamlined process for secure exchange of information was at least somewhat important to their workforce, social and biometric logins are a clear option to meet companies’ growing needs.
Streamlined UX and Security Don’t Have to be Antonymous
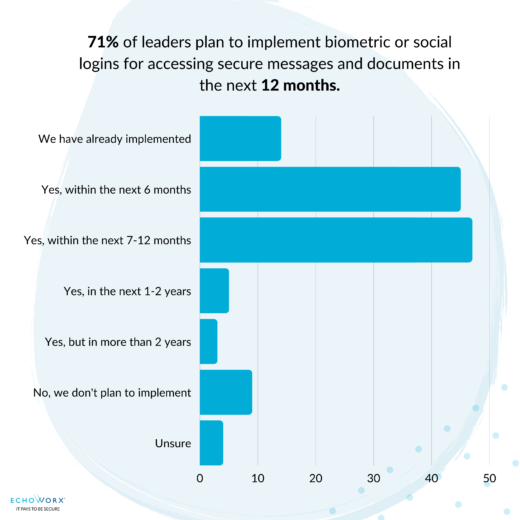
Implementing biometric and social login options is one way tech leaders are improving security while boosting efficiencies for their employees and customers. 71% of leaders reported that they plan to implement biometric or social logins for accessing secure messages and documents within the next 12 months.
With so much personal and business information online, reducing the complexity of staying secure is at the forefront of IT leaders’ minds – and for good reason. Using secure third-party social logins and biometrics is one-way employers are finding the balance between security, authentication, and ease of access – and is also one of the eight authentication options Echoworx currently offers.
Committed to providing customizable encryption options, Echoworx strives to accommodate global enterprises with configurable authentication and self-serve password controls that balance both user experience and security.
If you would like to learn more about how Echoworx can help you improve security and user experience by offering social login and biometrics, please reach out to book a demo with one of our encryption experts.
What You Should Do Now
- Discover how email encryption can enhance your business in various scenarios. Book your PERSONALIZED demo today.
- To understand the power of advanced email encryption, check out our Resources. It offers valuable guides, updates on strategies, and case studies of successful clients.
