All Resources

Echoworx Integration with DigiCert
Solution Brief: Discover how Echoworx integrates with DigiCert to streamline certificate encryption with auto-generated S/MIME credentials.

Echoworx Encryption Branding Overview
Demonstration: Echoworx empowers you to deliver secure, professional, and branded experiences in 28 languages. From encrypted emails to custom portals and notifications, tailor every touchpoint with your logos, colors, and messaging.
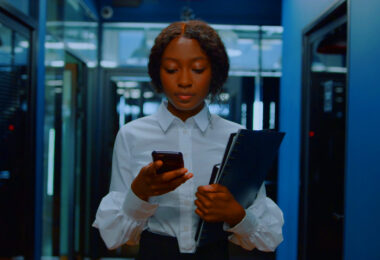
Echoworx Email Encryption
Solution Brief: Echoworx cloud-based encryption engineered for the modern enterprise. We don't force you to change your workflow or to compromise on usability. This is encryption that works with you, not against you.
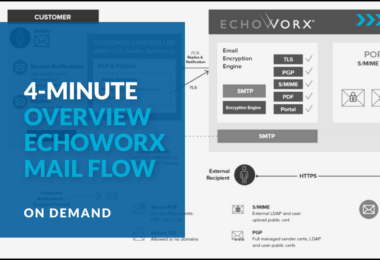
Echoworx Encrypted Mail Flow
Demonstration: Email security doesn’t have to disrupt your workflows. Echoworx is designed to integrate with your existing tools and processes, enhancing efficiency while providing robust, auditable encryption.

Echoworx Encryption Delivery Options
Demonstration: Email security is non-negotiable. Echoworx offers eight encryption delivery methods that make sharing sensitive information effortless and protected.

Echoworx Encryption: The Administrator’s Reality
Webinar: Technical discussion, for IT Administrators, about deploying and managing Echoworx's enterprise-grade encryption platform in a world governed by GDPR, NIS 2, and DORA.

Echoworx + Mimecast Integration
Solution Brief: Advanced email encryption made simple. Seamless security, effortless workflows, and enterprise-grade protection.
Echoworx Prepares for Quantum Computing
eBook: As quantum computing advances, encryption faces new vulnerabilities, pushing organizations to adopt post-quantum cryptography (PQC). Here’s a summary of our efforts to stay ahead in safeguarding encryption.

Echoworx + Proofpoint Integration
Solution Brief: Think advanced encryption. Intuitive user experiences. Scalable solution built for high-stakes enterprises.

Echoworx Security Assurance
Technology Brief: A comprehensive list of programs, certifications and accreditations claimed by Echoworx demonstrating our commitment to protecting your privacy.

Echoworx’s Authentication Options
Demonstration: Echoworx simplifies secure email access with customizable authentication options, including social login, two-factor authentication, and passwordless access.

Encrypting Email with Configurable Authentication
Webinar: Explores strategies for reducing password reliance, securing identities, and details Echoworx's authentication and access options for portal and file attachments.

Echoworx Encryption Delivery Options
Technology Brief: Learn about the range of secure delivery options provided by Echoworx Email Encryption, designed to meet different use case requirements with flexibility.

Evaluation Guide for Encryption Technology Decision Makers
Report: Learn how to identify whether an email encryption solution is appropriate to your organization and how to select one that best meets your needs.

Echoworx Technical Validation
Report: TechTarget’s Enterprise Strategy Group (ESG) has written this technical report detailing the evaluation of Echoworx’ user-focused email encryption capabilities for enterprises.

Five Trends Redefining Email Encryption
Webinar: Don’t just hope your encryption will keep pace. Get ahead. These trends aren’t coming. They’re already in RFPs, shaping buying decisions.

German Bank Builds Digital Sovereignty with Echoworx Cloud-Native Encryption
Customer Story: A major German bank needed to replace its legacy Totemo desktop encryption to meet strict DACH compliance. Discover the strategy they used to migrate to a cloud-native architecture, ensuring data residency and seamless integration with Mimecast and DigiCert to fortify their security for KRITIS and NIS2.

Echoworx Email Encryption Demonstration
Demonstration: We’ll cover features like system integration, branded secure messages, multiple delivery options, and easy access to encrypted emails and attachments.

Key Trends in Enterprise Encryption
Report: Encryption is evolving. Your secure communications should too. Discover the trends defining tomorrow's protection, today.

Migrate First-Wave Encryption to Echoworx
Webinar: We're covering the migration playbook for teams moving on to enterprise-grade managed SaaS encryption.
Migrate Totemo to Echoworx
Webinar: We’re peeling back the layers of a Totemo-to-Echoworx migration for the architects who have to make it work.

Migrate Zix to Echoworx
Webinar: If your team is weighing the costs of change versus the risks of standing still, this is for you.

Echoworx Migration Playbook
Playbook: Global leaders have already made the move to cloud-native encryption. Get the proven playbook and let our expert team do the heavy lifting.

Echoworx Encryption Explained
Video: Echoworx understands the complicated task of securely communicating because, encryption is all we do. See how Echoworx makes sending and receiving encrypted email easy.

10 Steps to Migrate PGP to the Cloud
Infographic: Echoworx offers seamless migration solutions for clients looking to transition their current PGP encryption systems from on-premises to the cloud. Explore the 10 steps to migrate your PGP to the cloud in this concise guide.

Migrate PGP Universal to Echoworx
Webinar: For all those moving on. We're covering the migration playbook for teams leaving PGP on-premises.

S/MIME Walkthrough and Demonstration
Webinar: Covers mail flow, certificate encryption, key management, API integration with trusted providers, and user experience for both senders and recipients.

Second Generation Enterprise-Grade Email Encryption: 2026 Guide
Guide: Defines the principles, architecture, and requirements; Use this resource to understand the transition from legacy systems to modern, dynamic email encryption (2025-2026).

The Role of Email Encryption in Secure Digital Business Processes
Showcase: Discover how leading organizations are leveraging email encryption to protect sensitive information, meet compliance standards, and build customer trust. Explore the benefits, challenges, and strategies for implementing a comprehensive email encryption platform.

Top Bank Mandates 2FA with Echoworx Cloud-Native Encryption Overhaul
Customer Story: A top-tier Canadian bank needed to replace its legacy Zix system. See the technical strategy they used to migrate to a cloud-native architecture that enforced mandatory 2FA, integrated with Proofpoint, and achieved data sovereignty with AWS.

Zix to Cloud-Native Migration
Video: Considering a similar move? This offers a practical look at how the migration was handled—what worked and what you can take away for your own planning.
