All Resources

Business Fit Report: Echoworx Email Encryption
Report: Learn what is required from encryption tools, architectural considerations to consider and how Echoworx’ approach to email encryption helps to meet the demands outlined in report.

Customer Success Stories
eBook: These encryption use cases are for the ones who won’t settle—who need beyond “good enough.”

Echoworx Integration with DigiCert
Solution Brief: Discover how Echoworx integrates with DigiCert to streamline certificate encryption with auto-generated S/MIME credentials.

Aligning with Business Leaders’ Top Priorities
Encryption Features: From avoiding passwords to enhanced registration security, our December feature updates are designed in response to customer requests and feedback from the Global 500 community. Dive into the full list now.

Echoworx Email Encryption
Data Sheet: Explore configurable encryption capabilities designed to help your organization address communication challenges.
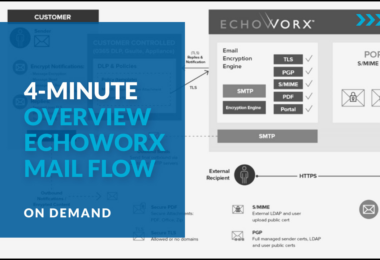
Echoworx Encrypted Mail Flow
Demonstration: Email security doesn’t have to disrupt your workflows. Echoworx is designed to integrate with your existing tools and processes, enhancing efficiency while providing robust, auditable encryption.

Echoworx + Mimecast Integration
Solution Brief: Advanced email encryption made simple. Seamless security, effortless workflows, and enterprise-grade protection.

Echoworx Prepares for Quantum Computing
eBook: As quantum computing advances, encryption faces new vulnerabilities, pushing organizations to adopt post-quantum cryptography (PQC). Here’s a summary of our efforts to stay ahead in safeguarding encryption.

Echoworx + Proofpoint Integration
Solution Brief: Think advanced encryption. Intuitive user experiences. Scalable solution built for high-stakes enterprises.

Echoworx Security Assurance
Technology Brief: A comprehensive list of programs, certifications and accreditations claimed by Echoworx demonstrating our commitment to protecting your privacy.

Email Encryption Advancements – A Guide
eBook: Explores the intricacies of the increasing need for advanced email encryption and draws insights from valuable feedback provided by the Global 500 community.

Echoworx Encryption Delivery Options
Technology Brief: Learn about the range of secure delivery options provided by Echoworx Email Encryption, designed to meet different use case requirements with flexibility.

Evaluation Guide for Encryption Technology Decision Makers
Report: Learn how to identify whether an email encryption solution is appropriate to your organization and how to select one that best meets your needs.

The Role of Email Encryption in Secure Digital Business Processes
Showcase: Discover how leading organizations are leveraging email encryption to protect sensitive information, meet compliance standards, and build customer trust. Explore the benefits, challenges, and strategies for implementing a comprehensive email encryption platform.

Echoworx Technical Validation
Report: TechTarget’s Enterprise Strategy Group (ESG) has written this technical report detailing the evaluation of Echoworx’ user-focused email encryption capabilities for enterprises.

Echoworx Email Encryption Walkthrough
Demonstration: We’ll cover features like system integration, branded secure messages, multiple delivery options, and easy access to encrypted emails and attachments.

Inside Echoworx + Mimecast’s Approach to Email Interoperability
Interview: TechTarget, Echoworx, and Mimecast break down email interoperability, smarter encryption, and seamless integration. Expert insights in under 30 minutes.

Echoworx Encryption Explained
Video: Echoworx understands the complicated task of securely communicating because, encryption is all we do. See how Echoworx makes sending and receiving encrypted email easy.

PGP Cloud Encryption – A Guide
eBook: Concise and practical guide explaining in detail your transition from PGP on-premises to a cloud-based solution.

10 Steps to Migrate PGP to the Cloud
Infographic: Echoworx offers seamless migration solutions for clients looking to transition their current PGP encryption systems from on-premises to the cloud. Explore the 10 steps to migrate your PGP to the cloud in this concise guide.

Encryption Success Stories, Insights from the Field
Webcast: Join our encryption experts for deep, firsthand discussions on real-world use cases—conversations you won’t get from a written brief or webpage.

S/MIME Walkthrough and Demonstration
Webinar: Covers mail flow, certificate encryption, key management, API integration with trusted providers, and user experience for both senders and recipients.

User Authentication: Understanding the Trends Shaping Email Encryption Access
Report: Discover the challenges and opportunities related to social logins and biometric authentication methods and learn how to set up user authentication without sacrificing ease of use.
