Does Increased Authentication Mean More Steps?

98% IT leaders reported their organizations need to step up authentication – yet over half are concerned about the detrimental business impacts brought by increased authentication processes, an Echoworx survey reveals.
While more locks might bring more security, they also bring more keys. Enter the email security conundrum, where companies leveraging digital delivery for more seamless service encounter this age-old conundrum: How do you increase security without decreasing message accessibility?
Digital acceleration drives email encryption adoption
As more organizations continue to migrate to paperless solutions, their need for secure digital lines of communications continues to increase. And, according to Ponemon’s the 2021 Global Encryption Trends Study, this increase is reliably steady, with 50% of survey respondents saying they have an encryption strategy applied across their entire organizational structure – a full 13-point increase since 2015. Another survey, 2021 Enterprise Encryption Needs And Experience Survey by Echoworx, lists exchanging secure digital documents as a primary driver for adopting secure communications solutions – as opposed to compliance-led drivers.
Concerns over user experience remain
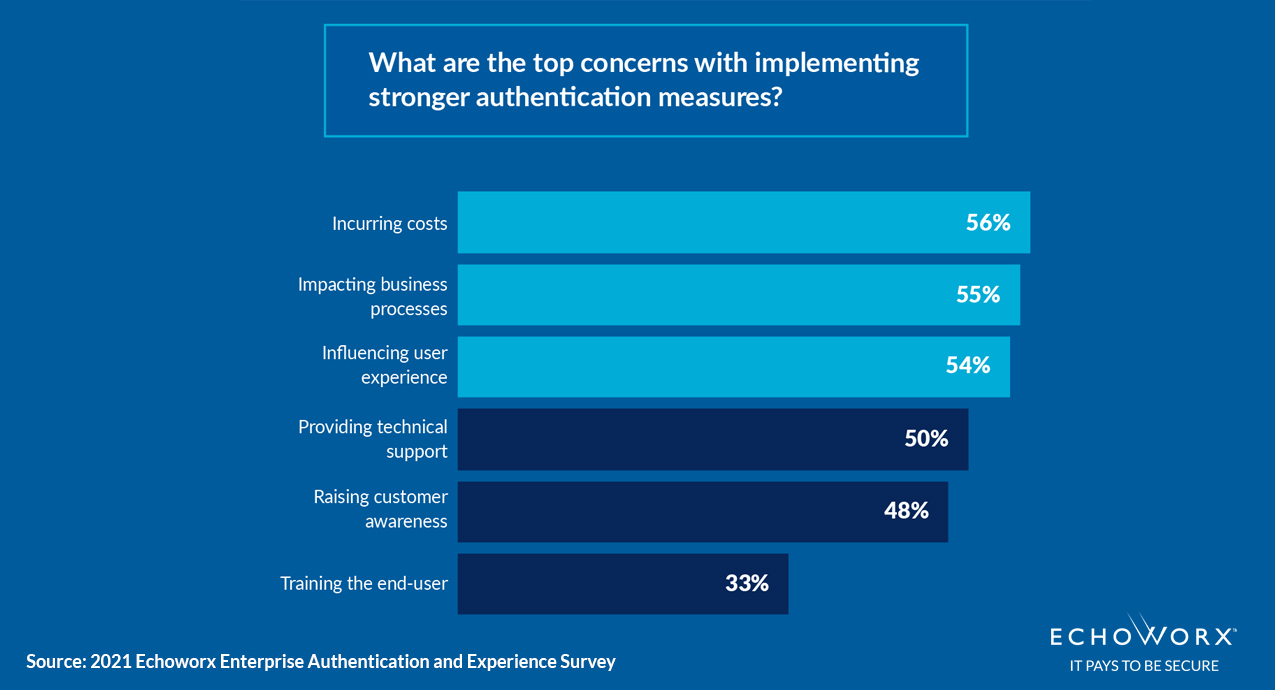
Digital is supposed to enable business, not hinder it. And, considering only 7% of IT leaders find it easy to protect email, despite 90% prioritizing email data protection, these concerns are not without basis. Our data shows that most concerns originate from user experience – with over 54% of IT leaders feeling impacting user experience as a roadblock.
Authentication experience front-and-centre
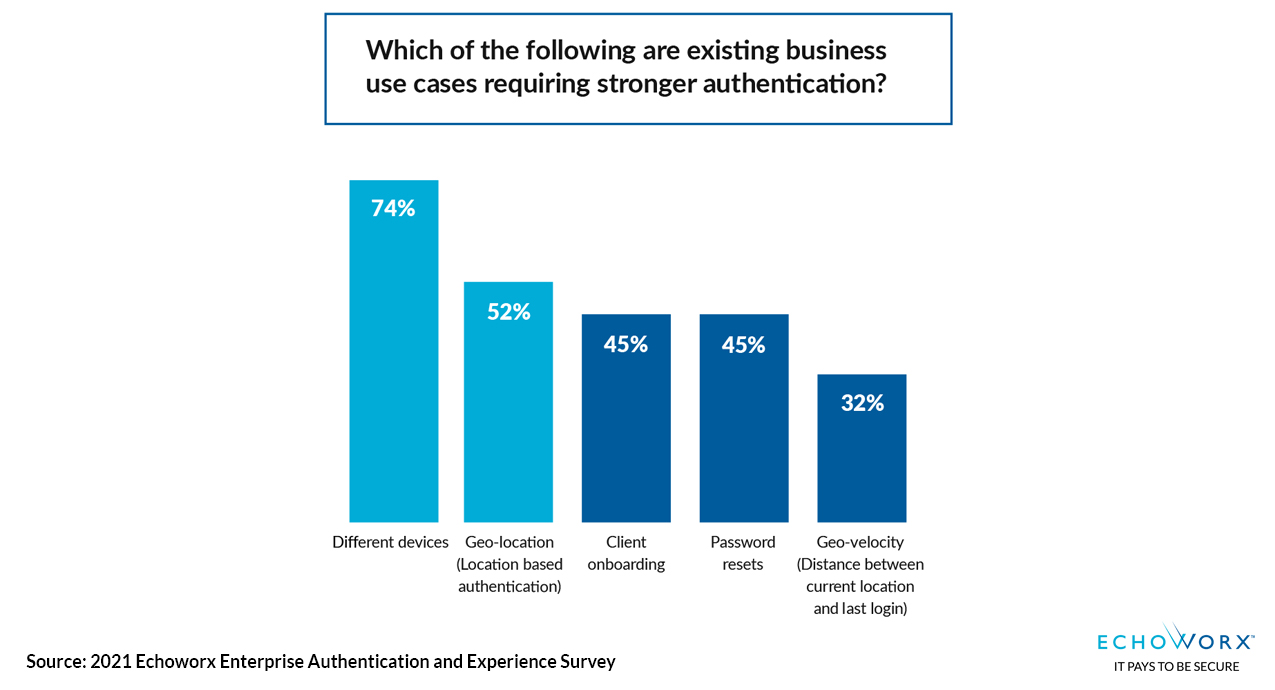
98% of IT leaders reported there is a need for hardened authentication measures. And yet, when most people think of increased authentication, they think of disconnected physical tokens, extra steps for users and endless clumsy password lists. For large organizations with customers numbering in the millions, user experience cannot be sacrificed, compromised or inconsistent across devices or geographical locations. Authentication options are necessary.
According to a Director, North American Retail Company “Customers will get turned around if only one option is presented to them and they aren’t familiar with it.”
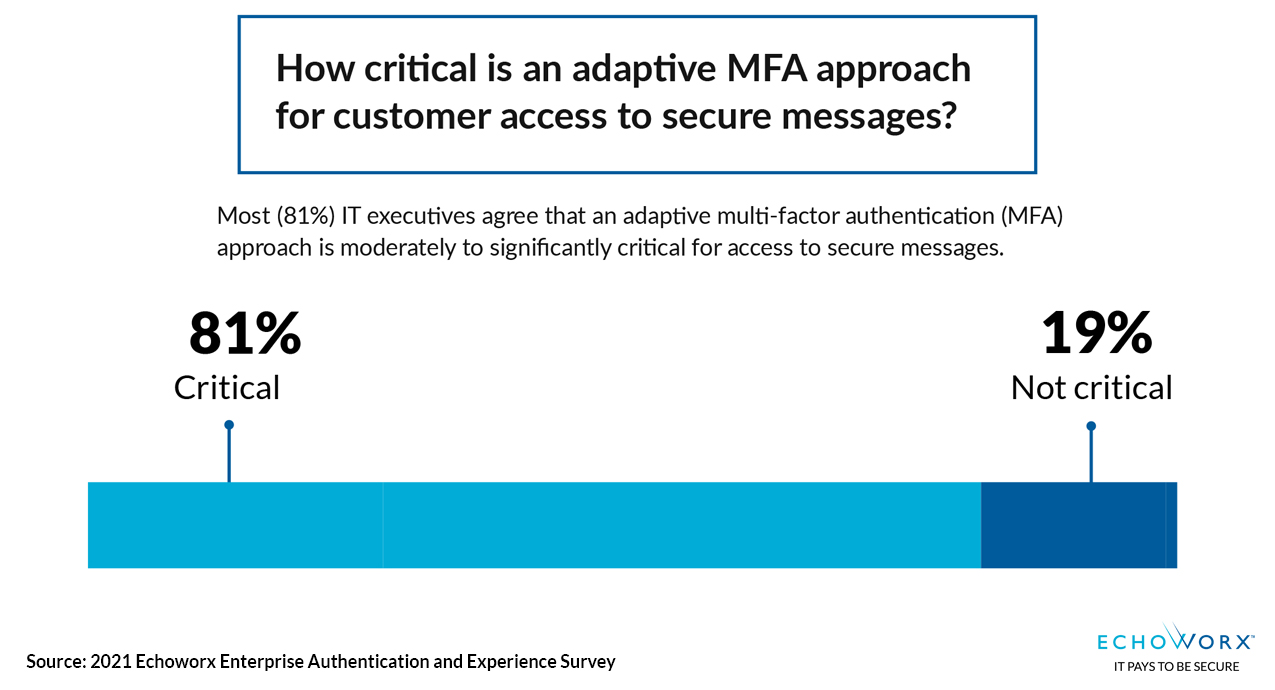
MFA popular for enhanced security
When it comes to email security, Echoworx found that IT leaders are most-focused on customer-centric flexibility – with 66% wanting to share protected email with anyone, anywhere and on any device. Yet 98% of survey respondents say they also need to prioritize increased authentication security to protect sensitive data. Multi-Factor Authentication (MFA) measures, referring to authentication processes requiring two or more authenticating pieces of information, like a user/password combination in addition to an automatic-generated One-Time Password (OTP), for example, are listed as critical to this process.
Biometrics promise passwordless experiences
Did you know the average employee spends 11 hours per year entering and resetting passwords? Biometrics, referring to authentication methods like fingerprint readers and facial recognition, might be the answer to a future without passwords – the ultimate streamlined authentication model. By leveraging existing built-in biometric technology on a user’s device, via web-standard APIs, like WebAuthn, organizations can leverage a device’s security to authenticate users without requiring additional information – removing the need for long, complex passwords.
“Eliminating the reliance on passwords is now a major objective for everyone offering online services,” said Andrew Shikiar, executive director and CMO of the FIDO Alliance.
More steps? Or just more options?
Does more secure authentication mean more steps? It depends. Just like not every customer is the same, neither is the data and documents organizations need to send and protect. The best authentication method is the one the user is most comfortable with. Authentication needs to be flexible enough to meet each unique business case. From increased authentication measures, requiring more steps, like MFA, to seamless, yet highly secure, passwordless methods, like biometrics, organizations need options in order accommodate every unique user demand.
“I believe there is a huge difference between privilege levels assigned to some, and not others, so we need varying levels of authentication.” Director of a North American Software Company
Echoworx features multiple authentication options
Featuring seven accepted methods to authenticate users, including biometrics and 2-Factor Authentication (2FA), a form of MFA, Echoworx provides both senders and receivers with more options and control over their experience. In addition to multiple ways to authenticate, Echoworx also enables access to eight secure delivery methods (Web Portal, S/MIME, PGP, TLS with fallback, PDF, PDF, Office and ZIP Secure Attachments), with support for up-to 27 languages.